The Heist
July, 2018

This year our daughter asked for a mystery game for her birthday. After considering a few different ideas, we settled on creating an art heist mini alternate reality game to play for her birthday party.
We envisioned creating the feeling of being in the middle of a James Bond or Jason Bourne adventure that everyone could participate in. We wanted puzzles and tasks that required group participation so no one person could dominate the experience that would last for the bulk of the party. We also needed to design and build the game quickly in the evenings without our kids noticing. Since we typically try to do something interesting for birthdays, they've started to expect that we are up to something and often poke around to figure it out.
Once we settled on an art heist, Beth sent out invitations for the party that mysteriously recruited each person to find their way to our house on our daugher's birthday and to look for "Larry's Donuts". They were also asked to RSVP with their codename.
We didn't actually have a game built, however. Over a few evenings we tossed around different ideas for possible parts of the game. As more ideas were shared, we were able to sequence them into a timeline that felt like a playable experience. We considered pulling in neighbors to be actors, but settled on driving the story thorugh messages and clues that didn't require interacting with other, actual people.
The premise of the story was that a Russian crime ring had been stealing famous paintings and reselling them on the black market. The party attendies had been recruited to join a secret team to track and retrieve the latest stolen painting before it was sold. To get the painting, the recruited spies would need to sort through clues, plant a listening device to intercept a secret meeting, hack people's cell phones, and go on a stake out.
We setup the secret headquarters in our downstairs family room. On the door we posted a sign for "Larry's Donuts" and left the arriving party members to find it and head downstairs.
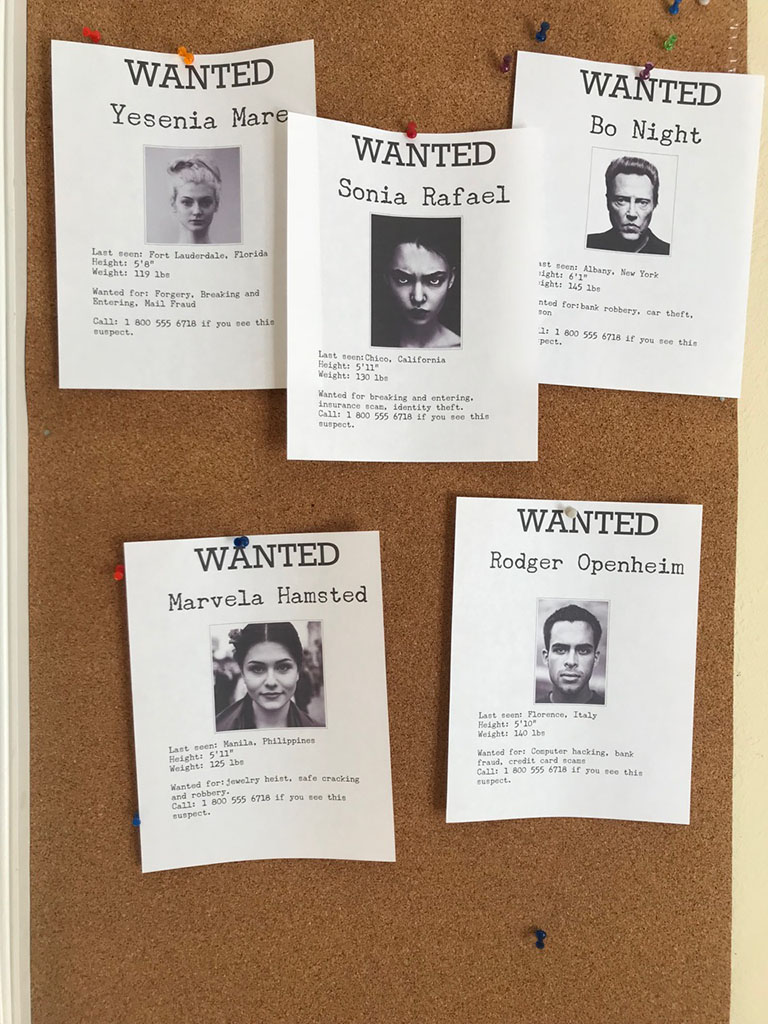
As they arrived, they found a computer terminal on a table and the walls covered in wanted posters.
Each attendee needed to sign in to the terminal with their codename and once everyone signed in, the game began.
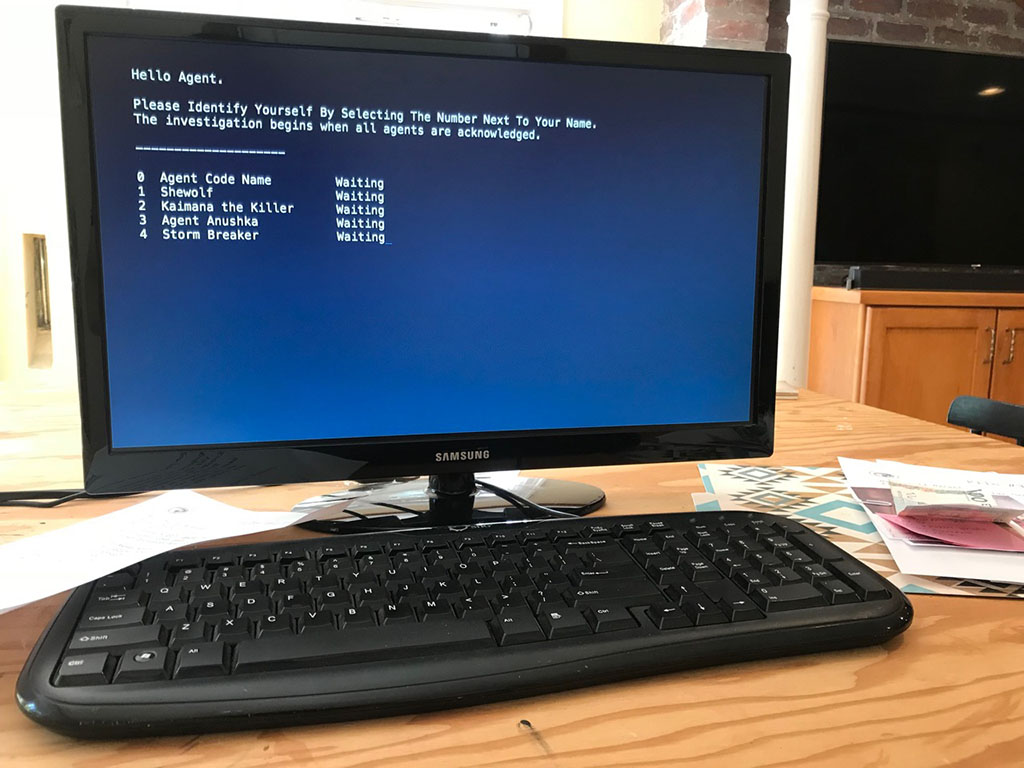
One of the largest challenges of building a game quickly like this is it can't really be play-tested. We had no idea how easy or hard each challenge would be or how long it would take. While editing the storyline we settled on being very explicit to tell players what to do, figuring that just tracking all the information and performing the tasks would be challenging enough. I used the computer terminal to act as the game's narrator to guide and pace their progress.
With little time to create a fancy, beautiful computer terminal, I settled on building something that looked and behaved like an old teletype terminal. All the text printed out as if it was arriving as a communication from some far off headquarters, complete with terminal beeps.
Occasionally "headquarters" would ask specific questions through the terminal and provide a menu of multiple choice options. I was worried that at some point a software bug might come up and crash the terminal. When The Last Pharaoh game was run, I learned that kids can mash buttons that can cause unexpected inputs that will crash the game. This time, I built a finite state machine to drive the transitions between each scene in the game and wrote progress to disk as the game was played. If the game ever crashed, it could be restarted right where they left off.
To start it off, Beth assembled a large dossier of known suspects complete with photos, newspaper articles, maps and other found items. Many of the suspects were noise and the first task was to sort through the collection to look for the possible thieves. We provided a corkboard to organize the clues and the kids quickly filled it. Included in one suspect's writeup was a web link to a newspaper. Beth created an online newspaper complete with articles and photos. Having just re-read Cryptonomicron and read about the playing card encryption algorithm, Beth previously included a key in the birthday invitation that mapped playing cards to letters. On the newspaper website, the paper published an interesting card game hand between several named people, much like how papers used to print bridge hands (do they still do that?).

It took just a bit of handholding to get the kids to see the web address in the dossier as an important clue. Once they got there, they found the card game and used their decoding key to translate a message and discover the names of the prime suspects. With that information, they used the terminal to tell headquarters the names.
For their next task, they decoded another card hand and learned that a secret meeting was to take place in a nearby park. Headquarters instructed them to retrieve a Remote Listening Device from a box of supplies, go to the park, plant the device and return before the suspects got there. Using the device they would be able to listen in on the meeting and hopefully discover more clues. I created a somewhat plausable device using some old electronics I had. To explain away that the device didn't seem to do anything, the instructions noted that to remain hidden, no lights or sounds would come from the device when activated.
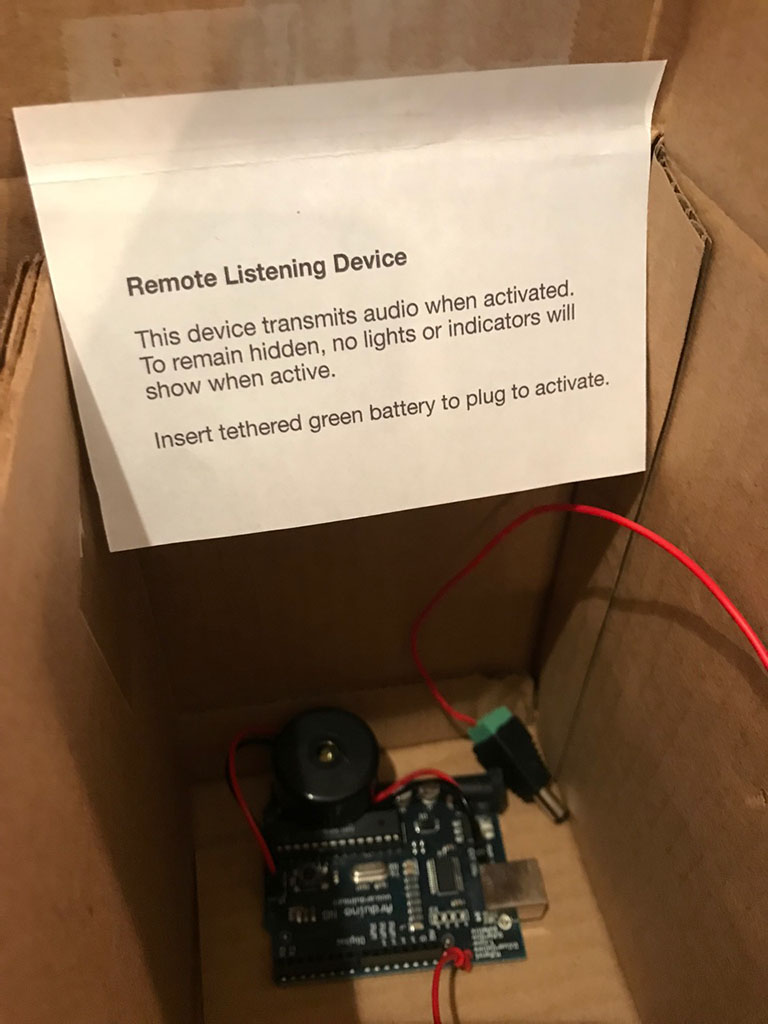
When the kids returned, they found the terminal waiting for them to confirm the placement of the device. Headquarters then explained the "signals group" was now redirecting satellites to connect to the device. After a bit, the signals group was able to lock on to the device and a signal was acquired! Headquarters then relayed the audio to the terminal so the players could listen in. Unfortunately the signal was not clear and only garbled conversations were audible, but the signals group was able to perform further analysis on the audio and make out the name of the location for the next meeting, which was close by.
Headquarters directed the players to split up and have half stake out the location, while the other half remained at the terminal. A pair of long range radios were in the supply box (the radios for my race car), so each group took a radio and set up for the stakeout. At the sametime, headquarters let the players know that they had tapped the cell phones of the suspects.
The group remaining back at the terminal were soon relayed a series of text messages between the subjects. The messages described that one of the suspects saw a group of people watching the location and that they needed to call off the meeting. The suspects agreed that they should instead immediately go retrieve the painting and escape because they had been discovered.
Ideally, the team at the terminal would have relayed these messages as they came in to the group at the stakeout. Unfortunately, we overestimated how long it would take players to reach the stakeout location, and so the messages started arriving several minutes too late. By that time, the entire group was talking about other things on the radios and missed the idea that they should relay the intercepted text messages over the radio. However, they did figure out near the end of the exchange that the painting was hidden at a nearby mailbox. Everyone then regrouped and ran to the mailbox to beat the suspects.
I taped a thrift store painting that Beth picked out under the neighborhood mailbox earlier in the day. The kids quicky discovered it wrapped in brown paper and brought it back.

When they returned, the terminal congratulated them on a job well done and let them know the painting would be returned to where it belongs... in a museum.
We were really happy with how The Heist turned out. We definitely confirmed that being explicit with instructions and basically just telling the players what to do next kept the pace moving and let the players make good, continued progress. If you want to play yourself, the code for the terminal is available on GitHub.